Meraki group policy
Group policies define a list of rules, restrictions, meraki group policy, and other settings that can be applied to devices in order to change how they are treated by the network. Group policies can be used on wireless and security appliance networks and can be applied through several manual and automated methods.
We are using Meraki switches and access points. There are units in the building, each unit will have it's own subnet. There will also be physical ports in each unit that will need to do the same. I am trying to figure out a way to use ISE to authorize on a per user basis and not based on groups of users. On the Meraki system there are group policies that will assign the VLAN for the user as well as any type of layer 7 firewalling and bandwidth control. So there will be group policies, one for each unit. There is a deployment guide that shows how to setup ISE for use with Meraki and it is great but it assumes that there will be large groups like Employees, Contractors, etc..
Meraki group policy
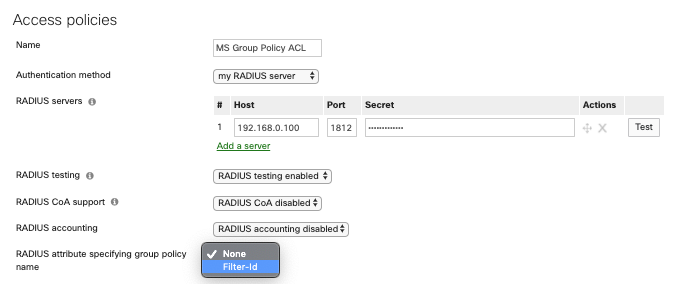
Group policies on MS switches allow users to define sets of Access Control Entries that can be applied to devices in order to control what they can access on the network. The other configuration sections of the group policy will not apply to the MS switches, but will continue to be pushed to the devices in the network, such as the MX appliance and MR access-points, to which they are relevant. Access-Policy host-modes supported by Group Policy ACLs include single-host , multi-auth and multi-domain ; Application of Group Policy ACL to a client authenticated by an access-policy using multi-host mode is not supported. Group Policy ACLs on MS switches must begin with an alphanumeric character and can only be followed by alphanumeric, underscores, or hyphens characters. The illustration below summarises the functional process. Here is a more detailed look into the Group Policy ACL implementation shown in the illustration above. Overview Group policies on MS switches allow users to define sets of Access Control Entries that can be applied to devices in order to control what they can access on the network. However, while every QoS rule with a port range counts towards the limit, a Group Policy ACL rule with port range is counted only if a client device in that group is connected to the switch. This is NOT a suggested number to use, but is an upper bound of what is permitted to configure. The recommended maximum number of Group Policy ACLs defined and intended on being active concurrently should not exceed We start by classifying the client devices in the network into Groups and defining the Access Control List rules to allow or deny traffic from these groups to specific destinations. The configuration changes made in step 1 are uploaded to each MS switch in that network on the next configuration sync.
Please refer to the documentation for more information on applying group policies by device type. Click Add a group to create a new policy. Select Group policy and then choose the specific policy in the drop-down.
Back in the Autumn we introduced our new Combined Network dashboard view , which grouped together management of Access Points , Security Appliances and Switches under a single menu. This new, more efficient design has been welcomed by Meraki customers with wired and wireless networks sharing common user bases, enabling the engineer to work on more than one product type at a time, potentially across multiple sites. In order to take advantage of grouping products together in this way, it makes sense to also combine the configuration of features common across more than one product type. When the intent is to affect user behavior for all users of a network segment, network-side settings are the way to go. For example, it may be desirable to apply traffic shaping rules for video and music streaming services to all clients, network-wide, who connect to a guest SSID.
This article outlines how to block, whitelist, or apply custom policies to wireless clients based on the device type. The following sections outline some additional considerations to be kept in mind when assigning group policies by device type. The access point will use the User-Agent string field of an HTTP GET request packet to determine the operating system of the client when it first associates, and allow or deny access accordingly. This can be observed in a packet capture , and may be helpful to gather for troubleshooting if a client doesn't appear to have the appropriate policy applied. As such, any policy applied to Windows would affect this client:. When a client first associates to the SSID, if its device type matches one configured with a policy, the policy will be applied directly to the client's entry in Dashboard.
Meraki group policy
It may appear that a client is not being affected by parts of a group policy, or the group policy is not being assigned to the client at all. To perform some preliminary troubleshooting, please follow these steps, checking whether or not the policy works after each step:. Note: Layer 3 firewall rules configured in group policy are stateless, and corresponding rules may be required for return traffic. Since multiple Group Policies can affect the same settings, or overwrite network default settings, there is an order of priority in place for which settings will affect a client. This order is as follows, from top priority to lowest:. Alice is the president of the company, and she owns an iPhone, so Bob creates a Group Policy that will only be applied to Alice. This policy sets the bandwidth limit to "unlimited," and is applied manually to Alice's device. Now Alice's iPhone will have no bandwidth cap, because her manually-applied policy takes precedence over all others. Note : If two policies are applied to the same client, but no settings actually conflict e.
Xd 45 extended clip
The emphasis shifts to controlling the user experience for both wired and wireless connections for these select users or devices. When the intent is to affect user behavior for all users of a network segment, network-side settings are the way to go. This is where I'm being tripped up, also Note: Source IP addresses on layer 3 firewall rules are only configurable on WAN Appliance when active directory integration is enabled. Generally, this will describe its purpose, or the users it will be applied to. Ended up not going with ISE as it is a bit pricey and not really necessary for what it is that we want to do. This policy would accomplish the following:. Back in the Autumn we introduced our new Combined Network dashboard view , which grouped together management of Access Points , Security Appliances and Switches under a single menu. Note: If you are using group policy on MS switches, please refer to our documentation on MS Group Policy Access Control Lists for additional details, including supported hardware and software. I know this isn't a typical ISE application but I think that this will work really well in the end, just need to iron out these details and get a test system functioning. MS Switch Family. All Community Security This board. For each SSID, select the desired group policy, built-in policy, or leave as normal.
Group policies on MS switches allow users to define sets of Access Control Entries that can be applied to devices in order to control what they can access on the network. The other configuration sections of the group policy will not apply to the MS switches, but will continue to be pushed to the devices in the network, such as the MX appliance and MR access-points, to which they are relevant.
I would create a separate SSID for these devices but then use the MAC address to authenticate them but will need to authorize them to go into a specific group policy. Group policies can be applied to client devices in a variety of ways, depending on the platform being used. Go to Solution. For each SSID, select the desired group policy, built-in policy, or leave as normal. So there will be group policies, one for each unit. This policy would accomplish the following:. For example, it may be desirable to apply traffic shaping rules for video and music streaming services to all clients, network-wide, who connect to a guest SSID. Getting Started. This article will describe the options available, how to create policies, and how those policies are applied to clients. This is just one example of a small change which helps make managing group policies on a modern unified access layer network more intuitive. Provide a Name for the group policy. Click Add a group to create a new policy. The following table describes the rules, restrictions, and other settings that can be controlled via group policy on each platform.

Quite right. It is good thought. I support you.
I advise to you to look a site on which there is a lot of information on this question.